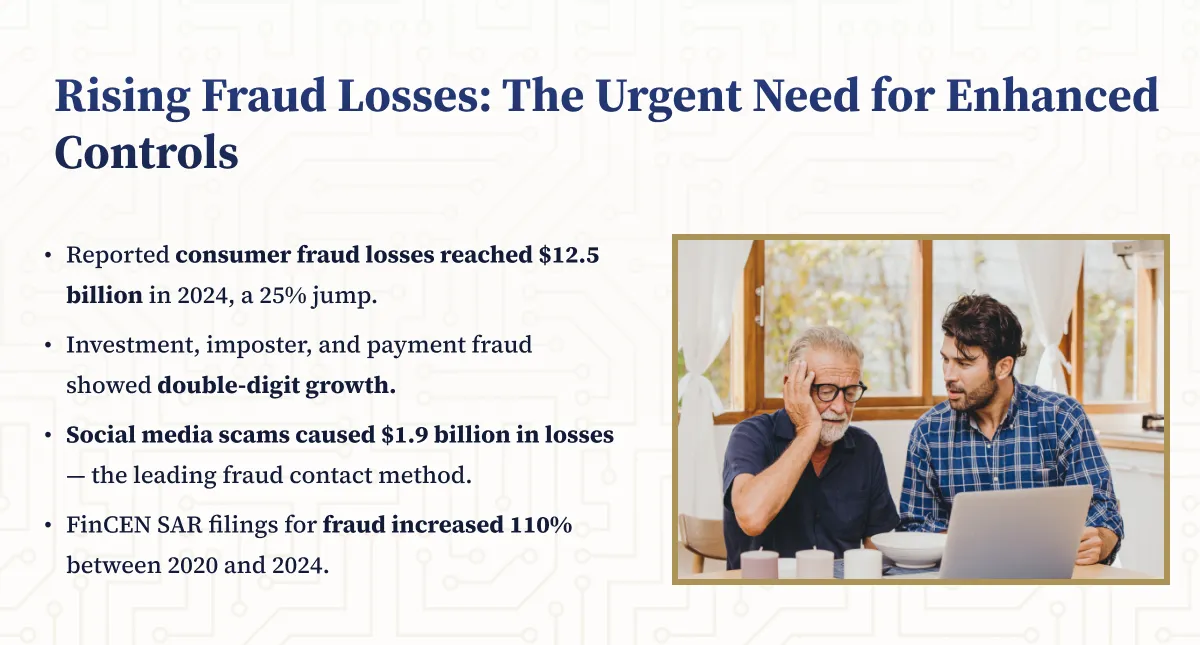
In today's rapidly evolving financial crime landscape, robust transaction monitoring systems and effective suspicious activity reporting (SAR) have become critical compliance components. As criminal methods grow more sophisticated and regulatory scrutiny intensifies, institutions failing to implement strong controls risk penalties, reputational damage, and exploitation by criminal elements.
The Evolving Financial Crime Landscape
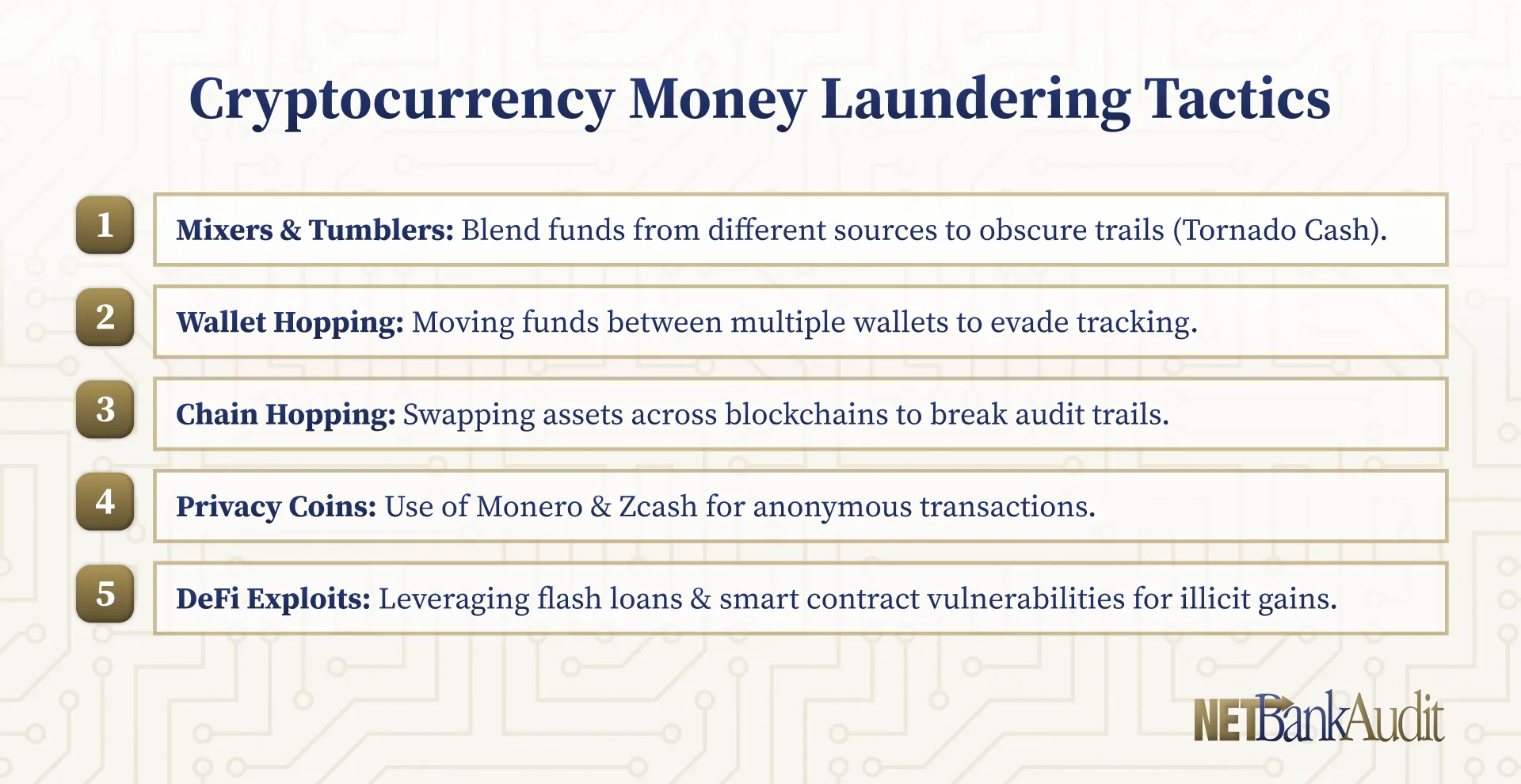
Today's financial criminals employ increasingly sophisticated techniques to evade detection, from complex layering schemes to cyber-enabled fraud. Digital assets and alternative payment systems have further complicated monitoring efforts.

The United Nations Office on Drugs and Crime estimates that 2-5% of global GDP ($800 billion to $2 trillion) is laundered annually, highlighting the importance of effective transaction monitoring and SAR processes. In 2022 alone, global fines for AML compliance failures reached $5.4 billion, underscoring heightened regulatory expectations.
Regulatory Framework for Transaction Monitoring and SAR
The Bank Secrecy Act (BSA) establishes core requirements for transaction monitoring and suspicious activity reporting. Under this framework, financial institutions must develop and maintain effective monitoring and reporting programs.
BSA Requirements for Transaction Monitoring
Financial institutions must implement systems reasonably designed to detect and report suspicious activity. The FFIEC BSA/AML Examination Manual guidance emphasizes that institutions should:
- Establish monitoring systems matching their risk profiles
- Implement both manual and automated monitoring processes
- Ensure monitoring covers all relevant products, services, and customers
- Establish appropriate thresholds and filtering criteria
- Subject monitoring systems to independent validation
These requirements recognize effective monitoring as the foundation for identifying potential money laundering, terrorist financing, and other illicit activities.
Suspicious Activity Reporting Obligations
Financial institutions must file SARs when they know, suspect, or have reason to suspect that a transaction:
- Involves funds derived from illegal activities
- Is designed to evade BSA requirements
- Has no apparent business or lawful purpose
- Is not consistent with the customer's normal activity
These requirements apply to transactions involving or aggregating $5,000 or more. Filing decisions must consider all relevant customer information and transaction history.
FinCEN regulations establish specific timeframes:
- Initial Filing: Within 30 calendar days from suspicious activity detection
- Extended Filing: Up to 60 days total if no suspect initially identified
- Continuing Activity: Follow-up SARs every 90 days for ongoing suspicious behavior
- Timing: 90-day period begins with filing of prior related SAR
Currency Transaction Reporting Requirements
Financial institutions must file Currency Transaction Reports (CTRs) for cash transactions exceeding $10,000 in a single day. Multiple cash transactions must be aggregated if conducted by or on behalf of the same person, including across different branches. Both cash-in and cash-out transactions must be aggregated separately, with CTR filing required if either exceeds $10,000. Read our full guide on CTR's here.

CTR Exemption Process
FinCEN allows institutions to exempt certain customers from CTR requirements:
Phase I Exempt Persons:
- Banks operating in the United States
- Government agencies and governmental entities
- Listed public companies and their majority-owned subsidiaries
Phase II Exempt Persons:
- Non-listed businesses that frequently conduct large currency transactions
- Payroll customers who regularly withdraw large cash amounts
For Phase II exemptions, institutions must file FinCEN Form 110, conduct annual eligibility reviews, renew exemptions biannually, and maintain comprehensive documentation.
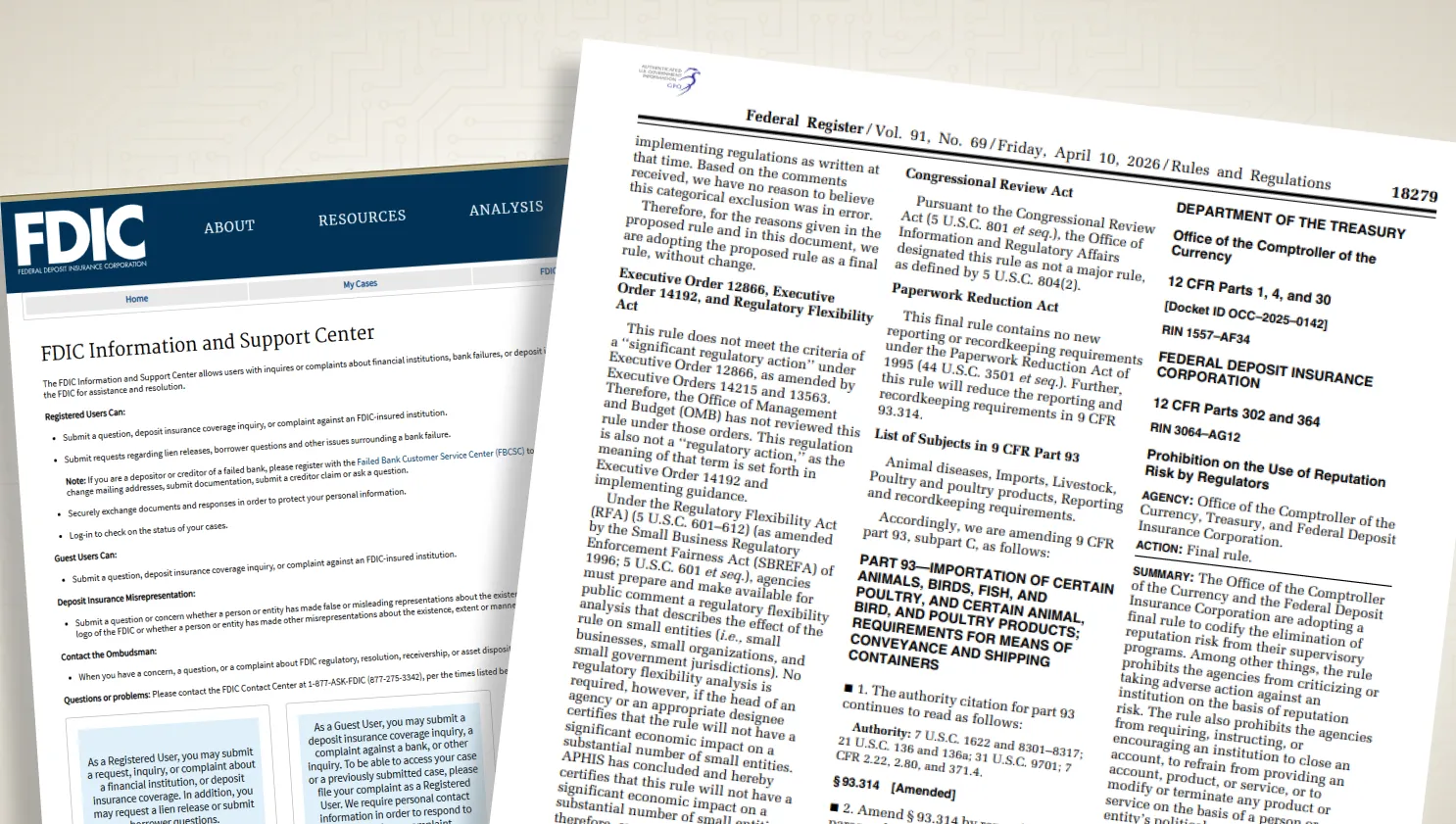
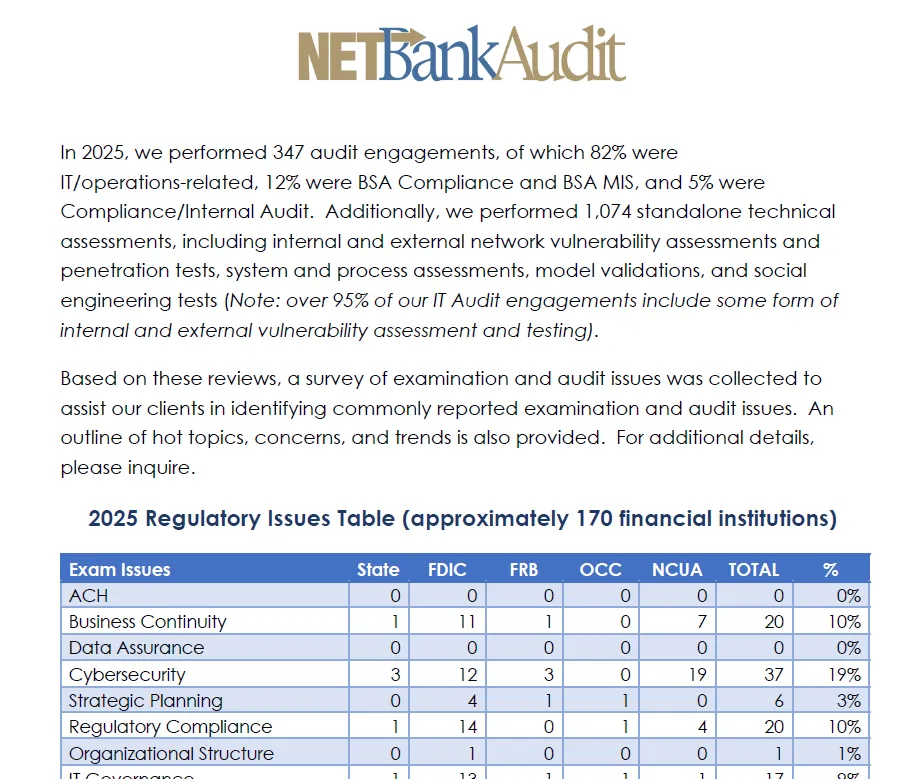
Regulatory Examination Focus
Regulatory examinations increasingly focus on the effectiveness of transaction monitoring and SAR processes. Examiners evaluate not just the existence of policies and procedures but their implementation and results. Key areas of examination focus include:
- The alignment between the institution's risk assessment and its monitoring approach
- The adequacy of staffing and technology resources
- The timeliness and completeness of investigations
- The quality of SAR narratives and supporting documentation
- The effectiveness of internal controls and governance
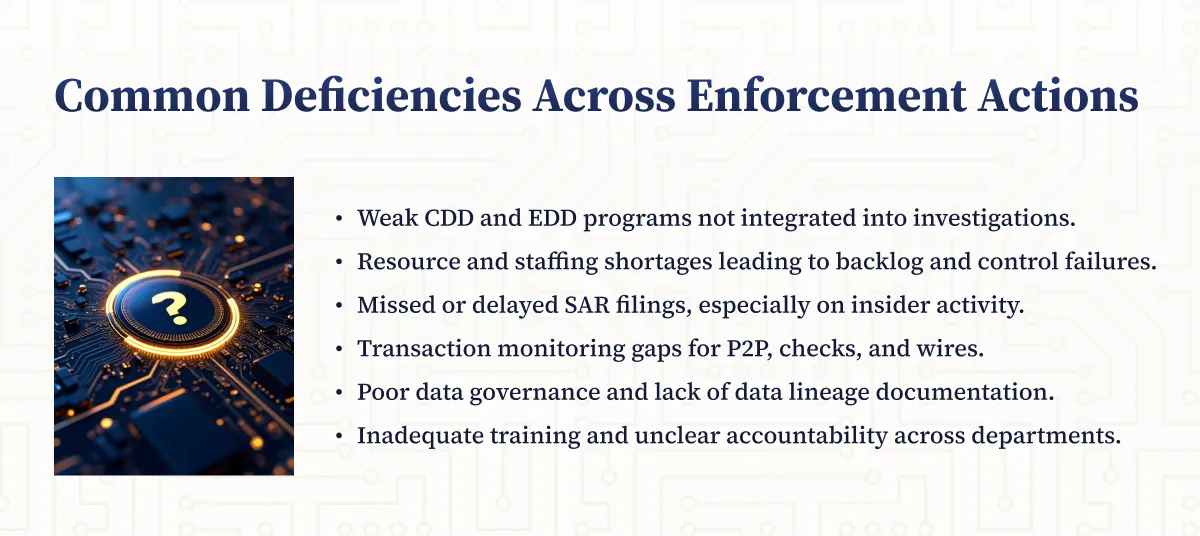
As outlined in FinCEN's Enforcement Actions, recent regulatory actions have highlighted deficiencies in transaction monitoring systems, inadequate staffing for alert investigations, and failure to file timely and complete SARs as common compliance weaknesses.
Policies, Procedures, and Processes for Identifying Suspicious Activity
A comprehensive framework for identifying suspicious activity begins with well-documented policies and procedures that clearly define responsibilities, communication channels, and operational processes. The following components are essential to an effective program:
Communication Channels and Referral Networks
Creating clear pathways for information flow is critical. Institutions should:
- Establish formal processes for front-line staff to report unusual activity
- Implement escalation procedures for significant concerns
- Develop protocols for regulatory and law enforcement communication
According to the FFIEC, "clear lines of authority and responsibility" form the foundation of effective monitoring and reporting systems.
Roles and Responsibilities for SAR Compliance
The designated individuals should possess the expertise, authority, and resources needed to fulfill their responsibilities effectively. The OCC Bulletin 2011-12 emphasizes the importance of appropriate governance and oversight for compliance processes, including transaction monitoring and SAR programs.

Here are the roles and responsibilities:
Monitoring Systems Utilized
Financial institutions should employ monitoring systems capable of identifying potentially suspicious transactions across all business lines and products. These systems typically include:
- Manual Monitoring: Reviews of transaction reports, customer activity logs, and exception reports by trained personnel
- Automated Surveillance Systems: Software that applies rules, thresholds, and analytics to identify unusual patterns or transactions
- Hybrid Approaches: Combinations of automated and manual monitoring tailored to the institution's size, complexity, and risk profile
The selection and configuration of monitoring systems should reflect the institution's specific risks, as identified through its BSA/AML risk assessment. According to a Thomson Reuters survey, 80% of compliance professionals cite increasing transaction volumes and complexity as significant challenges in effective monitoring, highlighting the importance of appropriate system selection.
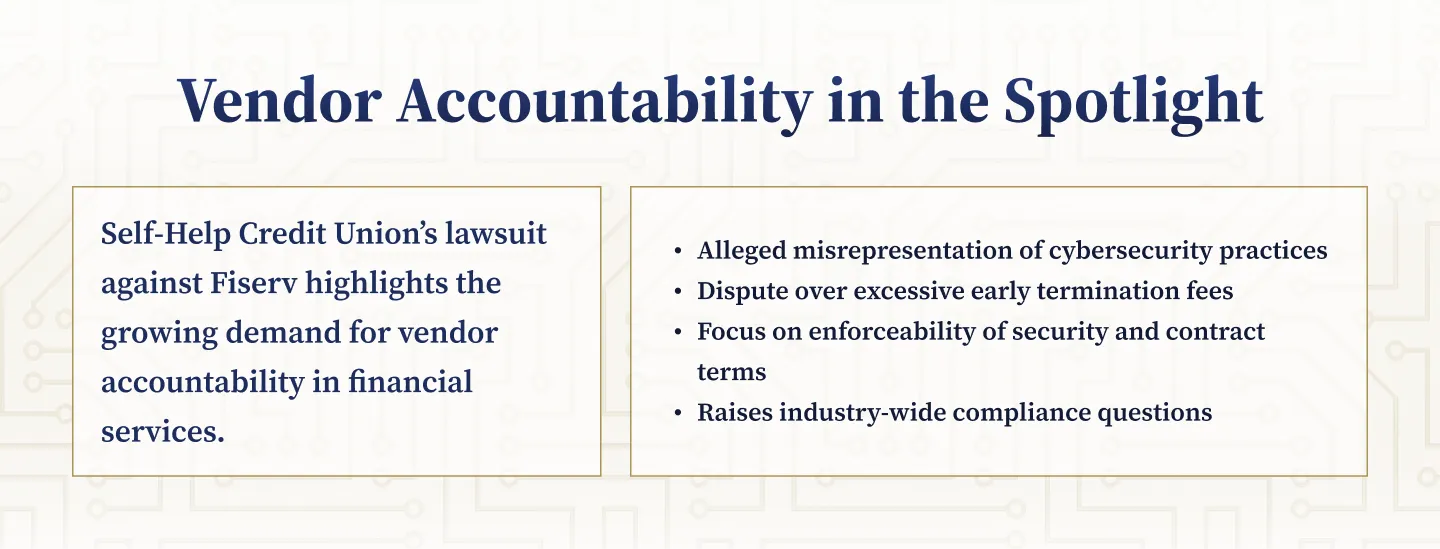
Procedures for Handling Law Enforcement Inquiries
Law enforcement inquiries often provide valuable information about potential criminal activity involving the institution's customers. Effective procedures should address:
- Processing and responding to subpoenas and National Security Letters
- Handling Section 314(a) information requests from FinCEN
- Evaluating whether law enforcement inquiries should trigger enhanced monitoring or SAR filings
- Maintaining confidentiality of law enforcement information
These procedures should ensure prompt, accurate responses while protecting sensitive information. The FinCEN Advisory on Maintaining Effective AML Programs emphasizes the importance of information sharing between financial institutions and law enforcement in combating financial crime.
Independent Validation and Oversight
Regular independent validation of monitoring systems and processes helps ensure their continued effectiveness. Key elements include:
- Testing the accuracy and completeness of data feeds
- Validating the appropriateness of monitoring scenarios and thresholds
- Assessing the adequacy of staffing and other resources
- Reviewing the quality and timeliness of investigations
- Evaluating the consistency and appropriateness of SAR filing decisions
This validation should be conducted by individuals independent of the BSA/AML function, such as internal audit staff or qualified external consultants like NETBankAudit. The results should be reported to senior management and the board, with action plans developed to address any identified weaknesses.
Transaction Monitoring Systems
Effective transaction monitoring systems, whether manual or automated, serve as the first line of defense in identifying potentially suspicious activity. These systems must be carefully designed, implemented, and maintained to ensure they reliably detect unusual transactions and patterns.

Transaction Monitoring Approaches
Financial institutions typically employ a combination of monitoring approaches based on their size, complexity, and risk profile.
Manual Monitoring
Despite technological advances, human oversight remains essential. Front-line employees often detect suspicious behavior that automated systems might miss, such as customer nervousness or inconsistent transaction explanations. According to the FFIEC, "banks with a lower risk profile may find that a manual monitoring system is sufficient" if it covers all relevant risk areas.
Key manual monitoring activities include reviewing exception reports, observing customer interactions, conducting relationship manager reviews, and maintaining branch-level oversight.
Automated Surveillance
For larger or more complex institutions, automated systems provide necessary scale and consistency. These systems apply pre-defined rules to identify unusual transactions, compare activity against expected profiles, flag transactions meeting risk criteria, and generate alerts for investigation.
Effectiveness depends on proper configuration and data quality. Institutions must calibrate systems to their specific risks and update them regularly to address emerging threats.
System Methodology and Validation
Whether manual or automated, monitoring systems should employ methodologies that align with the institution's specific risks:
- Risk-Based Approach: Apply enhanced scrutiny to higher-risk customers, products, and geographies
- Appropriate Thresholds: Establish thresholds based on customer segmentation and expected activity
- Relevant Scenarios: Create monitoring scenarios aligned with known typologies and risk assessment
- Efficient Alert Management: Implement processes to prioritize alerts effectively
Regular independent validation is essential. Key validation elements include data integrity checks, scenario testing, threshold analysis, and backend testing to identify false negatives. This validation should be conducted by personnel independent of the BSA/AML function.
Access controls should include role-based permissions, formal change management procedures, comprehensive audit trails, and proper segregation of duties.
Managing Alerts and Investigations
Effective alert management is crucial for successful suspicious activity identification. Institutions must establish processes for timely review, thorough investigation, and well-documented decisions.
%20Works.webp)
Alert Review and Investigation
Prompt review of alerts is essential for meeting regulatory timeframes. Institutions should establish:
- Alert generation schedules based on risk and volume
- Initial review timeframes (typically 24-48 hours)
- Risk-based prioritization to ensure high-risk situations receive prompt attention
- Procedures to monitor and address any backlogs
Investigation should include reviewing customer information, analyzing transaction patterns, obtaining clarification when necessary, and consulting external sources for context. All steps and information should be thoroughly documented to support decisions and demonstrate compliance.
Referral Processes and Staffing
Clear referral channels help ensure comprehensive monitoring. Standard forms, staff training, referral tracking, and appropriate feedback loops contribute to an effective program.
Adequate staffing with appropriate expertise is essential. Institutions must ensure sufficient personnel for normal operations plus surge capacity, appropriate skill levels, ongoing training, and clear performance expectations.
Decision-Making and Account Management
SAR filing decisions require careful evaluation of all available information. Effective decision processes include:
- Consistent criteria for determining whether activity meets filing thresholds
- Multiple perspectives on complex decisions, often through a SAR committee
- Clear documentation of rationale, especially for decisions not to file
- Enhanced monitoring for customers with previous suspicious activity
For significant or ongoing suspicious activity, institutions should consider whether continuing the customer relationship is appropriate. Establish closure criteria, apply policies consistently, document decisions thoroughly, and follow formal exit procedures. Institutions should ensure de-risking decisions are based on individual risk assessments rather than categorical exits.
%201%20(1).svg)
%201.svg)
THE GOLD STANDARD INCybersecurity and Regulatory Compliance
Suspicious Activity Reporting (SAR) Process
A well-designed SAR process ensures timely, accurate, and complete reporting of suspicious activities to appropriate authorities.
SAR Completion and Filing
Effective SAR filings require:
- Timeliness (30 days from detection, with extensions as permitted)
- Complete and accurate data in all fields
- Clear, concise narratives addressing essential information
- Comprehensive supporting documentation
Creating Effective SAR Narratives
The narrative section provides context and details that structured fields cannot capture.

According to FinCEN guidance, effective narratives should:
Answer fundamental questions:
- Who conducted the suspicious activity?
- What instruments or mechanisms were used?
- When and where did the activity occur?
- Why is the activity suspicious?
- How did the suspicious activity take place?
Follow best practices:
- Present information chronologically
- Use simple, direct language without jargon
- Remain objective and factual
- Clearly distinguish financial data
- Reference supporting documentation
- Avoid disclaimers and copy-pasted policy text
The narrative quality directly impacts law enforcement's ability to investigate effectively.
Governance and Recordkeeping
Keeping board and senior management informed about SAR filings is both a regulatory requirement and governance best practice. Provide regular filing summaries, escalate significant issues promptly, identify resource needs, and engage leadership in policy reviews.
Comprehensive recordkeeping includes maintaining SAR copies for at least five years, retaining all supporting documentation, documenting non-filing decisions, and ensuring secure storage.
SAR Confidentiality Framework
SAR confidentiality is mandated by federal law (31 U.S.C. 5318(g)(2)). Institutions must:
- Safeguard all SAR-related information
- Restrict access to personnel with legitimate need
- Train staff on confidentiality requirements
- Implement robust technical safeguards
Federal law prohibits notifying any person involved in a reported transaction about a SAR filing and restricts disclosure of SAR information by any current or former institution personnel.
The law provides a "safe harbor" (31 U.S.C. 5318(g)(3)) protecting institutions from liability for good faith reporting, but this doesn't override confidentiality requirements.

Permitted Information Sharing
Despite strict confidentiality requirements, certain controlled sharing is permitted:
Within the Organization: Information may be shared with personnel having a legitimate need to know.
With Parent Companies and Affiliates:
- U.S. depository institutions may share with head offices and controlling companies
- Sharing with domestic affiliates engaged in SAR filing is permitted
- Sharing with foreign affiliates is generally prohibited
With Authorities: SAR information may be provided to FinCEN, appropriate law enforcement and supervisory agencies, and officials with proper legal authority. Financial institutions may share SARs with regulatory examiners for supervisory purposes.
All sharing must be documented, with recipients informed of confidentiality requirements.
Transaction Testing and System Effectiveness
Regular testing and validation help ensure continued program effectiveness. A comprehensive approach examines both design and operational effectiveness.
Testing Approach
Effective testing serves multiple purposes:
- Assessing regulatory compliance
- Evaluating suspicious activity detection effectiveness
- Identifying control weaknesses
- Validating system changes
Appropriate sample selection is critical. Focus on higher-risk areas, ensure coverage across business lines, use statistically valid methods, and address previous deficiency areas.
Comprehensive testing should examine:
- System configuration and rule effectiveness
- Alert generation accuracy
- Investigation quality and consistency
- Decision appropriateness
- Documentation adequacy
- Regulatory timeframe compliance
Purpose of Transaction Testing
Transaction testing serves multiple important purposes in the compliance program:
- Assessing Compliance: Determining whether activities comply with regulatory requirements and internal policies
- Evaluating Effectiveness: Measuring how well processes identify and report suspicious activity
- Identifying Weaknesses: Finding gaps or deficiencies that require remediation
- Validating Changes: Ensuring that system or process modifications achieve intended results
These objectives align with regulatory expectations for ongoing program assessment. The FFIEC BSA/AML Manual - Appendix O provides detailed guidance on transaction testing methodologies and objectives, emphasizing the importance of risk-based approaches.
Sample Selection Criteria
Effective testing relies on appropriate sample selection that reflects the institution's risk profile. Key considerations include:
- Risk-Based Focus: Concentrating testing resources on higher-risk customers, products, and geographies
- Coverage Requirements: Ensuring appropriate coverage of all significant business lines and transaction types
- Statistical Validity: Using sample sizes and selection methods that provide meaningful results
- Previous Findings: Focusing additional attention on areas with previous deficiencies
Sample selection should be documented and justified based on the institution's risk assessment and testing objectives. This documentation helps demonstrate the adequacy of the testing approach to internal stakeholders and regulatory examiners.
Testing Procedures
Comprehensive testing procedures examine all aspects of the transaction monitoring and SAR processes:
- System Configuration: Verifying that monitoring systems include appropriate rules and thresholds
- Alert Generation: Confirming that alerts are generated for activities that meet defined criteria
- Investigation Quality: Assessing the thoroughness and accuracy of alert investigations
- Decision Appropriateness: Evaluating whether decisions to file or not file SARs were reasonable and consistent
- Documentation Adequacy: Reviewing the completeness of investigation and decision documentation
- Timeliness: Measuring compliance with internal and regulatory timeframes
These procedures should be tailored to the institution's specific processes and technologies. NETBankAudit's independent testing services offer customized testing programs that address each institution's unique risks and compliance challenges.
Areas of Focus
Testing should focus on areas that present the greatest compliance risks and have the most significant impact on suspicious activity identification:
- Alert Management: Reviewing the handling of system-generated and manually identified alerts
- Investigation Depth: Assessing whether investigations gather and analyze all relevant information
- SAR Quality: Evaluating the accuracy, completeness, and clarity of filed SARs
- Governance Effectiveness: Examining board and management oversight of the SAR process
- Resource Adequacy: Assessing whether staffing and technology resources are sufficient
The specific focus areas should reflect the institution's risk profile, previous testing results, and any recent changes to processes or systems.
Assessing System Effectiveness
Beyond technical compliance, testing should evaluate whether transaction monitoring systems effectively identify potentially suspicious activity:
- False Negative Analysis: Reviewing transactions that did not generate alerts to identify potential missed suspicious activity
- False Positive Assessment: Analyzing alert closure rates to identify potentially excessive false positives
- Typology Coverage: Confirming that monitoring scenarios address all relevant money laundering and terrorist financing typologies
- Emerging Risk Adaptation: Evaluating how well systems adapt to new threats and typologies
These assessments provide valuable insights into the overall effectiveness of the monitoring program and identify opportunities for enhancement. According to the OCC Bulletin on Model Risk Management, regular validation of monitoring systems is essential for ensuring their continued effectiveness in a changing risk environment.
Integration of Advanced Analytics and AI
As financial crime becomes more sophisticated and transaction volumes continue to grow, advanced analytics and artificial intelligence offer powerful tools for enhancing transaction monitoring capabilities. These technologies can improve detection accuracy, reduce false positives, and increase overall efficiency.
Leveraging Advanced Analytics and AI
Modern analytics and AI technologies can transform suspicious activity detection capabilities. These tools offer advantages over traditional rule-based monitoring:
- Enhanced Detection: Machine learning identifies subtle patterns conventional systems miss
- Reduced False Positives: Better pattern recognition improves alert quality
- Operational Efficiency: Automation frees staff for complex investigations
- Adaptability: Systems evolve to address emerging threats
While regulators support technological innovation, they expect:
- Sound model risk management
- Explainable decision-making processes
- Regular validation and testing
- Continued human oversight
Implementation challenges include data quality requirements, system integration complexity, specialized skill needs, and significant investment costs. Institutions should carefully assess these factors when considering advanced analytics solutions.
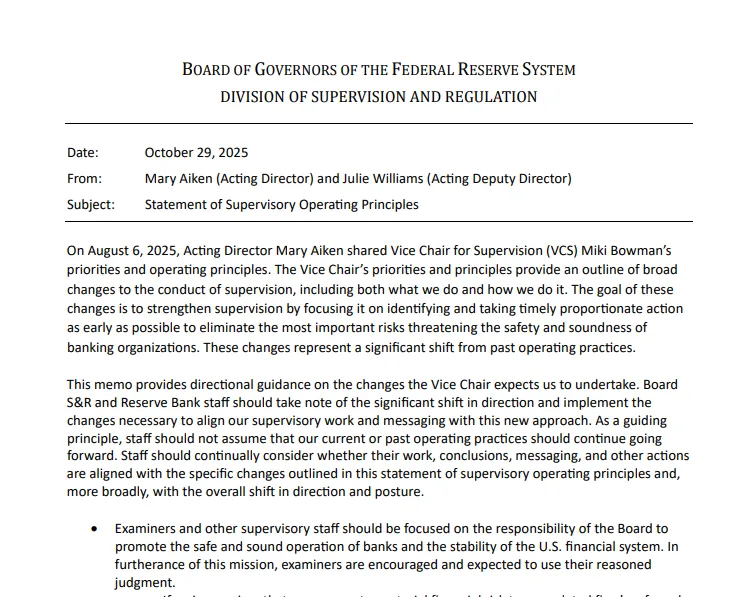
Staff Training and Compliance Culture
Employee Training
Comprehensive training ensures all employees understand their suspicious activity identification responsibilities. Effective programs include:
- Role-specific content tailored to job functions
- Regulatory knowledge and compliance importance
- Red flag recognition techniques
- System usage training
- Documentation standards
The FFIEC emphasizes that "all appropriate personnel" must understand their reporting responsibilities.
Culture of Compliance
A strong compliance culture reinforces suspicious activity detection throughout the organization:
- Visible leadership commitment from senior management and board
- Clear ethical conduct and regulatory compliance expectations
- Adequate staffing, technology, and training resources
- Accountability incorporated into performance evaluations
- Open communication channels for raising concerns
The Federal Reserve guidance emphasizes that "a strong compliance culture is essential for effective risk management."
Regulatory Examination and Enforcement Trends
Examination Priorities
Recent regulatory examinations have focused on several key areas:
- Alignment between risk assessment and monitoring approach
- Transaction monitoring model validation
- Alert investigation timeliness and quality
- SAR narrative completeness and clarity
- Technology and system governance
The FFIEC BSA/AML Examination Manual provides detailed procedures and expectations to guide internal assessments.
Enforcement Trends
Recent enforcement actions highlight common deficiencies:
- Inadequate monitoring coverage across products or customers
- Insufficient staffing for alert review
- Poor documentation of investigations and decisions
- Late SAR filings
- Inappropriate monitoring thresholds and scenarios
Proactive preparation for examinations should include conducting self-assessments, organizing documentation, developing effectiveness metrics, addressing known weaknesses, and preparing key personnel.
Build a Sustainable Compliance Program with NETBankAudit
In today's environment of evolving financial crime threats and heightened regulatory expectations, effective transaction monitoring and SAR processes are essential. Financial institutions must build sustainable frameworks that protect against both financial crime and regulatory penalties.
Key Success Factors
Successful programs share several common characteristics:
- Risk-Based Approach: Aligning monitoring with specific institutional risk profiles
- Adequate Resources: Providing sufficient staffing, technology, and training
- Effective Governance: Establishing clear accountability at all levels
- Continuous Improvement: Regularly assessing and enhancing program elements
- Documentation Discipline: Maintaining comprehensive compliance records
As financial crime techniques evolve, institutions must continually enhance their transaction monitoring and SAR capabilities. This ongoing journey requires commitment, expertise, and adaptability to changing circumstances.
NETBankAudit offers comprehensive services supporting institutions at every stage, from program design through ongoing validation. Our experienced compliance professionals can help assess current processes, develop enhanced policies, implement effective governance, train staff, and prepare for regulatory examinations.
Contact NETBankAudit today to learn how our tailored solutions can strengthen your transaction monitoring and suspicious activity reporting programs.
.avif)

.svg)
%201.webp)



.webp)
%20(1).webp)

.webp)

.webp)
.webp)
.png)

.webp)

.webp)











.webp)



.webp)

%201.webp)
.webp)
%20(3).webp)


.webp)



.webp)




.webp)
%20(1).webp)

.webp)










.webp)
.webp)

.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
%201.svg)